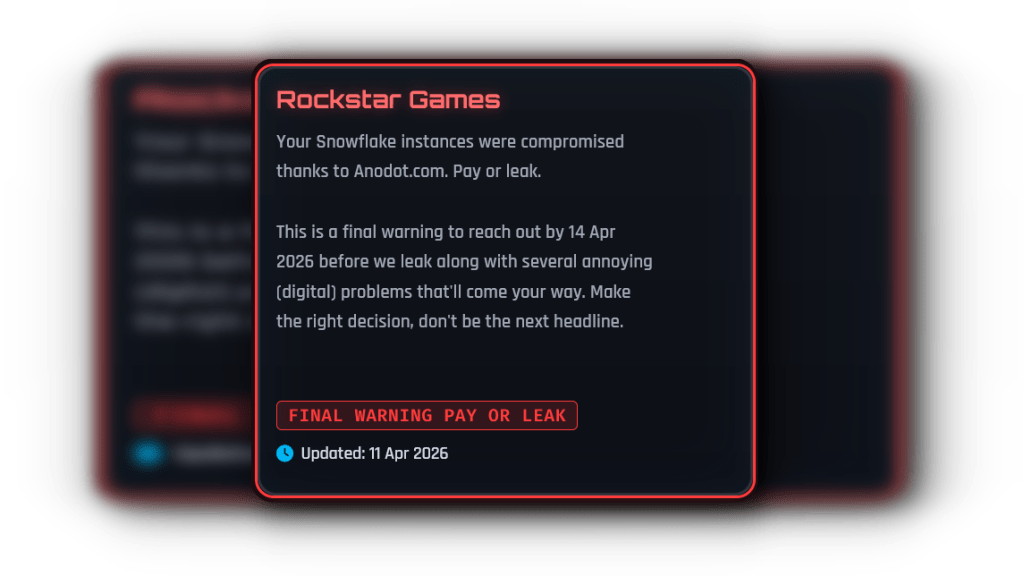
I saw the ransom image before the press release landed: neon text ripped from a game menu, menacing and oddly playful. You feel that same cold when a company you trust is told to pay or watch secrets leak. I knew then this was not theatre — it was leverage.
I’m following the ShinyHunters claim that they breached Rockstar Games and are holding company data for ransom. The group says it slipped past defenses by exploiting a flaw in Anodot, an AI analytics tool, and used the stolen authentication tokens to move through Rockstar’s Snowflake data warehouse. The resulting ransom demand came with a graphic pulled straight from Cyberpunk 2077, a flourish meant to mock and to intimidate.
On my feed: Rockstar says players won’t notice — but the intrusion happened anyway
Rockstar confirmed a breach to Cyber Security Guru and asserted that players would not be affected. I’ve read that line before after other incidents; it’s meant to calm you while engineers sweep the mess.
The core of this incident, if the reporting holds, is not a shaky server or weak password. It’s third-party software that sits inside corporate telemetry. Anodot is designed to track cloud spending and telemetry in real time; that level of access gives it tokens and permissions that can be as powerful as admin credentials. The authentication tokens ShinyHunters claim to have taken were a master key to the kingdom.
How did ShinyHunters breach Rockstar Games?
ShinyHunters reportedly exploited a vulnerability in Anodot, then used the legitimate authentication tokens to access Rockstar’s Snowflake data warehouse. Because the access came through valid tokens, traditional monitoring can miss the activity until abnormal volumes or exfiltration are spotted.
At eye level: the ransom note looked like a game UI rather than corporate extortion
The image was styled straight out of Cyberpunk 2077, complete with neon typography and a game-like layout. It’s an odd choice for a criminal notice; it’s also an intentional signal to anyone who remembers GTA leaks.
Using a branded, pop-culture visual is psychological leverage — it frames the attack as performance and threats as spoilers. The group has history: ShinyHunters has taken responsibility for breaches at Microsoft, Wattpad, and AT&T. That track record raises the stakes: this is not a bluff, it is a pattern.
Is my data at risk after the Rockstar hack?
Rockstar says player systems are not impacted, but data theft and leakage don’t always show up as service outages. If customer records, internal documents, or unreleased media were in the Snowflake warehouse, those assets can be copied and redistributed without touching game servers.
In plain sight: third-party integrations are a recurring weak point
I’ve watched security teams wrestle with vendor access for years; third-party tools deliver convenience and attack surface at the same time. That tradeoff is visible in this case.
Snowflake is a widely used data warehouse and Anodot is one of several monitoring tools that require broad permissions. When a vendor has visibility into billing, logs, or telemetry, attackers who compromise that vendor can pivot to dozens of customers. The ransom demand is the fast-money angle; the bigger risk is persistent access or staged leaks of intellectual property, such as development footage of GTA 6, which has leaked before.
What is Anodot and Snowflake, and why do they matter?
Anodot is an AI-driven analytics platform that spotlights anomalies in cloud usage and costs; Snowflake is a cloud data warehouse used to store large datasets. Both are common in enterprise stacks. When tools like Anodot sit with high privileges, they become targets because their tokens let attackers move laterally without raising immediate alarms.
As someone who tracks these incidents, I’ll warn you: the script we’re watching now repeats across industries. Security teams must scrutinize vendor token scopes, rotate credentials, and apply anomaly detection that looks for unusual queries, not just failed logins. Microsoft, Wattpad, and AT&T were previous chapters in ShinyHunters’ playbook — each one a reminder that permission creep is an invitation.
The ransom image is a neon scar across a corporate announcement, a pop-culture taunt meant to be shared as evidence of control. You can call it intimidation; I call it leverage delivered with flair. With GTA 6 months from release, the timing raises commercial and reputational pressure you can practically feel.
I’ll keep watching the threads: what Rockstar discloses next, how Snowflake and Anodot respond, and whether any files actually surface. Are companies treating the permissions of their monitoring tools as critical infrastructure, or as optional conveniences?
Who pays, who resists, and who decides what the public has a right to see — which side will you believe when the leaks start appearing?
